Threat Researcher focused on monitoring and analyzing wide spectrum of sources by utilizing HUMINT, SOCMINT, and OSINT and producing finished threat intelligence.
-

0+
Conference Talks Delivered
-

0+
years of progressive cybersecurity experience
-
0+
citations on 2 academic research papers

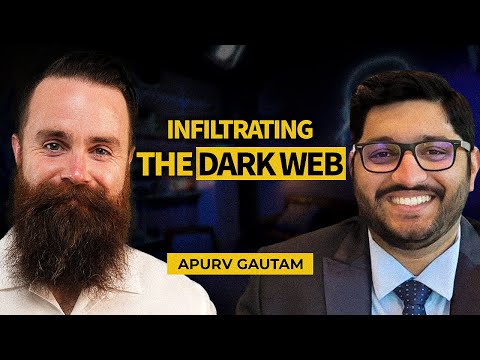
Apurv Singh Gautam is a Security Analyst specializing in anti‑scraping investigations to protect Meta products and users from automated abuse, data exfiltration, and AI‑enabled threats. He focuses on detecting and disrupting scraping operations at scale by analyzing large datasets, building automation, and conducting investigations using OSINT, external threat intelligence, and internal telemetry to drive high‑impact enforcement actions.
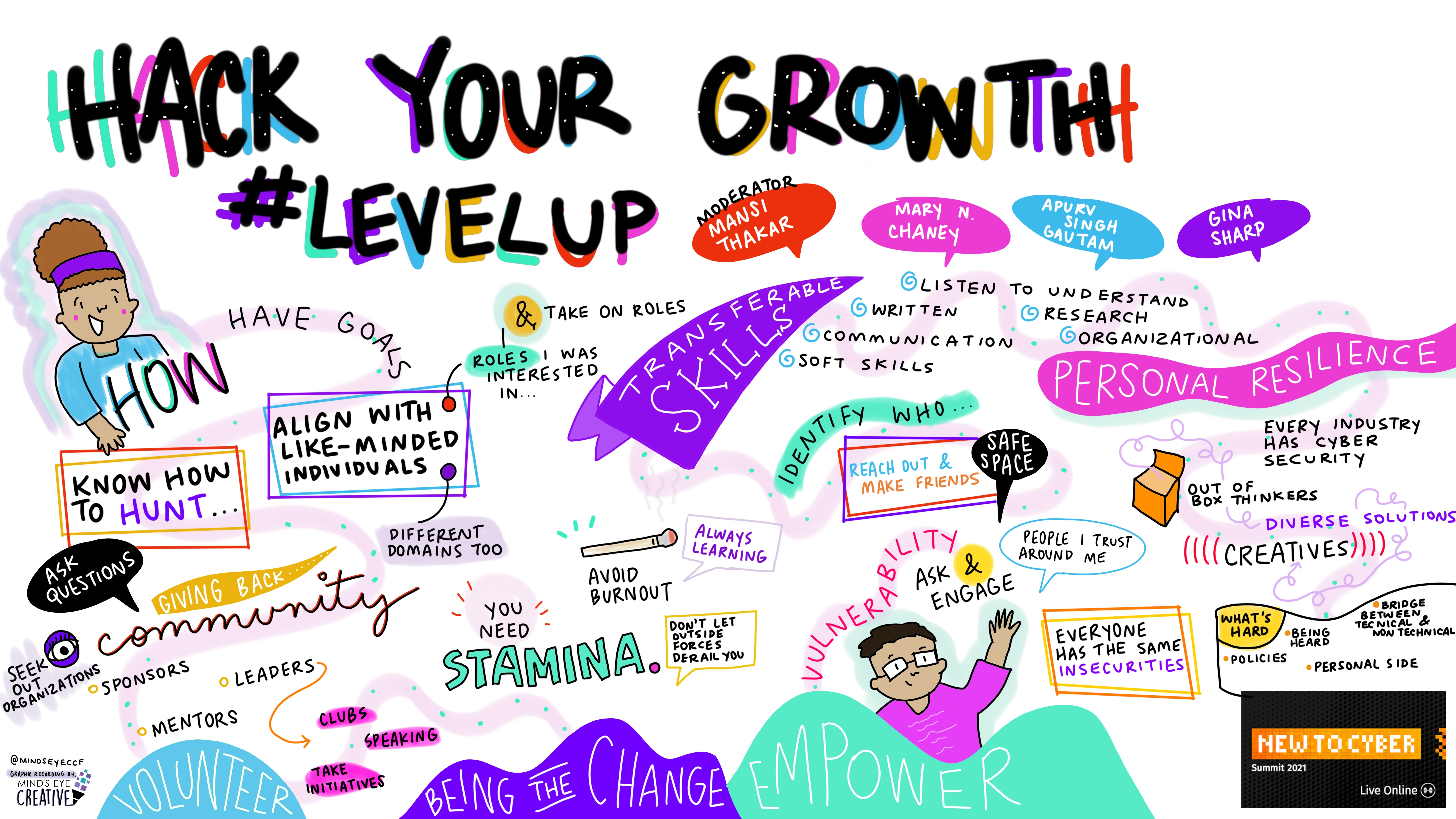
Apurv has contributed to the latest SANS Institute's course FOR589 on Cybercrime Intelligence and is a contributing member of Curated Intel. He has delivered talks & workshops at national and international conferences like SANS OSINT Summit, SANS Cyber Defense Forum, DEFCON Blue Team Village, BSides Singapore, RootCon and others. Apurv is featured in major podcasts like ITSPMagazine, Tech Talks with Singh, etc. He is passionate about giving back to the community and helping others get into this field, and has delivered many talks and workshops in schools and colleges. In the past, he has volunteered with StationX to help students navigate into Cybersecurity, and also volunteered as a Darknet researcher at CTI League and EBCS Darknet Analysis group. He holds a master's degree in Information Security from Georgia Institute of Technology, USA.
He looks forward to the end of the day to play and stream one of the AAA games, Rainbow 6 Siege.
Invited Talks & Podcasts (Cybersecurity)
-
-

-

Singh in USA - Mar 2025
PodcastThe Dark Truth About Cybersecurity in 2025! (Ft. AI Threat Intel Expert)
-

ITSPMagazine - Off the Record with Saman — Student Abroad Podcast - Mar 2024
PodcastGeorgia Tech Unveiled: Tales of Admission Triumphs | Conversations with a Current Student & an Alum
-

-

-

-
Invited Talks & Podcasts (MS in USA)
-

YudiJ - Jul 2020
PodcastCareer, Scope, And Future of Cybersecurity! Job Roles in Cybersecurity! Ft. Apurv
-

YudiJ - Jun 2020
PodcastHow to do Masters in USA Under $5000 - Ft. Apurv | How to get Funding for Education in America
-

GREedge - Oct 2019
Guest Seminar304 In GRE: Georgia Tech & 4 Other Top Admits: Get Apurv's Strategy
Recorded Talks
-

-
-

SANS Cyber Defense Forum - Oct 2020
TalkAutomating Threat Hunting on the Dark Web and other nitty-gritty things
-

Defcon 28 Red Team Village - Aug 2020
TalkAutomating Threat Hunting on the Dark Web and other nitty-gritty things
-

Other Talks, Workshops, & Seminars
-
-
-

Symbiosis Institute of Technology (SIT) - Apr 2019
SeminarAll about Cyber Security - From the Perspective of an MS Student
-
-

-
The Aryan International School (TAIS) - Jul 2017
Seminar2-Day Seminar on Cybersecurity Fundamentals

-
Cyble Inc.
Sr. Threat Research Analyst
Austin, USA
(Apr 2023 - Nov 2025)
Highlights of my work:
- i. Responding to Requests for Information (RFI) and providing tactical and operational intelligence analysis to address clients' priority intelligence requirements
- ii. Serve as Subject Matter Expert (SME) for Generative AI projects in Threat Intelligence, developing proof-of-concept (POC) solutions to innovate and refine new ideas
- iii. Collaborating with experienced, globally diverse, cross-cultural teams world wide to aid the collection, processing, analysis, and production of threat intelligence
- iv. Leveraging and curating advanced OSINT, SOCMINT, and HUMINT investigations into actionable intelligence to provide context-driven, automated and manually enriched threat intelligence
- v. Creating timely intelligence deliverables, key trends, and advisories enriched with IOCs (indicators of compromise) and TTPs (tactics, techniques, and procedures) tailored to specific industries and prospective customers' needs
- vi. Assisting with threat monitoring and continuous tactical alerting regarding emerging threats identified within darkweb forums, telegram chanels, and other private group messengers
-
Cyble Inc.
Threat Researcher
Austin, USA
(Jul 2021 - Mar 2023)
Highlights of my work:
- i. Conducted surface and dark web investigations, profiled threat actors & criminal groups, and researched malware & ransomware attacks
- ii. Led the US-based client requests by performing continuous monitoring and alerting regarding emerging threats to the clients and their specific industry
- iii. Produced concise finished intelligence reports for new findings within the surface and dark web related to our global customers
- iv. Acted on the ad-hoc requests by global clients and produced detailed intelligence reports in the form of tactics, techniques, and procedures (TTPs)
- v. Utilized OSINT, SOCMINT, and HUMINT in leveraging new threat information from the surface and dark web
- v. Designed and developed small-scale Python scripts to assist with automation of collection, processing, and storage of data and reducing the time load by 40%
-
IZON Group LLC
Security Analyst
Atlanta, USA
(Sept 2020 - Mar 2021)
Highlights of my work:
- i. Created multiple crawlers/scrapers for collecting large scale data from the surface/dark web forums
- ii. Analyzed data in the form of TTPs and ingested it in elasticsearch
- iii. Visualized data in Kibana in the form of threat intel feeds and created dashboards
-
International Computer Science Institute (ICSI), UC Berkeley
Security Research Intern
Berkeley, USA
(May 2020 - Jul 2020)
Highlights of my work:
- i. Conducted deep dive analysis of malicious data from 4-5 dark web forums/markets
- ii. Analyzed large unstructured datasets using advanced NLP algorithms (LDA, CatE)
- iii. Generated 6 high-level threat intelligence metrics for the analyzed data
-
Volon Cyber Security Ltd.
Security Researcher
Pune, India
(May 2018 - May 2019)
Highlights of my work:
- i. Performed advanced open source intelligence (OSINT) on surface web and dark web sites
- ii. Analyzed threat landscape on dark web forums and markets
- iii. Designed an advanced automated scraping tool to scrape data using Python Scrapy
- iv. Accomplished scraping unstructured data of 20+ dark web forums and markets and ingested into elasticsearch
- v. Conducted human intelligence (HUMINT) on the dark web forums and marketplaces
-
Georgia Institute of Technology
M.S. in Cybersecurity
-
Symbiosis Institute of Technology
B.TECH in Information Technology

-
Applying Threat Intelligence Metrics on the Dark Web Data
The exponential growth in data and technology has brought in prospects for progressively destructive cyber-attacks. Traditional security controls struggle to match the intricacy of cybercriminal tools and methods; organizations have shifted towards Threat Intelligence - evidence-based knowledge, including context, mechanisms, indicators, implications, and actionable advice, about an existing or emerging menace or hazard to assets that can be used to inform decisions regarding the subject's response to that menace or hazard. Amongst various platforms for threat intelligence (TI), hacker forums deliver rich metadata and thousands of Tools, Techniques, and Procedures (TTP). Today, many public and commercial sources distribute dark web threat intelligence data feeds to support this purpose. However, our understanding of this data, its characterization, and the extent to which it can meaningfully support its intended uses are still quite limited. This research will address these gaps by defining a set of metrics for characterizing dark web threat intelligence data feeds. There have been similar metric-based research done for structured data, but there is no prior work for free-form text. Our measurement results give grounding to the consumers about the purchase and optimal use of dark web threat intelligence data feeds.
-
Hacker Forum Exploit And Classification For Proactive Cyber Threat Intelligence
The exponential growth in data and technology has brought in prospects for progressively destructive cyber-attacks. Traditional security controls are struggling to match with the intricacy of cybercriminal tools and methods, and organizations are now looking for better approaches to strengthen their cybersecurity capabilities. Cyber Threat Intelligence (CTI) in real-time is one such proactive approach that ensures that deployed appliances, security solutions, and strategies are continually evaluated or optimized. Amongst various platforms for threat intelligence, hacker forums deliver rich metadata, and thousands of Tools, Techniques, and Procedures (TTP). This research paper employs machine learning and deep learning approach using neural networks to automatically classify hacker forum data into predefined categories and develop interactive visualizations that enable CTI practitioners to probe collected data for proactive and timely CTI. The results from this research show that among all the models, deep learning model RNN GRU gives the best classification results with 99.025% accuracy and 96.56% precision.
-
Recent Trends in the Era of Cybercrime and the Measures to Control Them
This chapter illustrates the understanding of cybercrime, recent trends in cybercrime, and the measures by which these cybercrimes can be eliminated to a considerable extent. The authors discuss various emerging cybercrime techniques, including steganography, next-generation malware, next-generation ransom wares, social engineering attacks, and attacks using machine learning and IoT devices. This chapter is published as Chapter 10 in the book Handbook of e-Business Security.
For more projects checkout my GitHub
-
Robin is an AI-powered tool for conducting dark web OSINT investigations. It leverages LLMs to refine queries, filter search results from dark web search engines, and provide an investigation summary.
-
A curated list of OSINT Tools for the Dark Web.
-
This is a research project that uses the top 1 million list of domains from three data sources, namely Majestic, Alexa, and Tranco, to apply a set of security metrics and visualize the results of that analysis along with a summary of the change in popularity of domains for 30 days. The project also provides a tool to enumerate sub-domains efficiently, without compromising on quality results.
-
A reverse shell over HTTP (dodges deep packet inspection) by using Python 3 and no external dependencies.